Even though OpenVPN Access Server is primarily geared towards individuals looking to link their corporate networks and clients together, OpenVPN Access Server can be configured to connect your clients to a private network. This setup is valuable when your clients have specific application discovery requirements and need a simple way to allow complete bidirectional connectivity between all of these clients.
This private network is developed internally inside the OpenVPN Access Server instance itself, this setup will work under environments where discovery services are usually prohibited. For example, Amazon AWS, VPS providers, collocation, and other data center locations.
What is a Virtual Private Network?

A virtual private network offers you an encrypted connection to your network over the internet. Businesses protect their information by storing it within a private network. This possibly a server or computers on-premises or cloud-hosted services. For the importance of securing information, the network should be secured, which means secret.
When you use a virtual private network, you extend that private network, making it virtual. This way, remote workers can securely connect to the business’s network by using a virtual private network connection over the internet. This can be done securely, continuing to keep the business’s data confidential by encrypting those connections.
Through a virtual private network, packets are sent over the internet through an encrypted tunnel. This tunnel makes it come out as though you are directly connected to your business’s private network. Nowadays, people use VPN services for other purposes such as masking the IP and encrypting internet traffic, mainly for privacy reasons, securing important data when connecting from the public network, or bypassing restrictions or firewalls.
Potential uses of this virtual private network include:
- Accessing services that depend on broadcasts or multicasts such as Apple’s Bonjour
- Accessing Local Area Network services such as printers and file sharing.
- Sharing the VPN connection with virtual emulators and machines.
- Playing local area network games over the internet.
- Networking virtual machines and emulators with old computers that use such non-IP protocols.
- Using non-IP protocols such as IPX over wireless or the internet.
The OpenVPN Access Server can be set up on-premises with your own server. In this blog, TechNinjaPro will focus on the configuration of OpenVPN Access Server for a Privately Bridged Network.
Prerequisites
To configure OpenVPN Access Server to utilize private bridging, all of the requirements must be met:
- Your Access Server app is running on a platform that supports Ethernet Bridging.
- Your OpenVPN supports the TAP Ethernet Bridging functionality.
- Your network server must be in layer 2 Ethernet Bridging Mode.
- Your network server must not be running Multi-Daemon mode. The UDP protocol is powerfully preferred over the TCP protocol in VPN
- The internet tunneling choice is VPN settings should be turned off.
- The bridge-utils package is set up on OpenVPN Access Server. For example, an empty bridge is built upon a system startup.
- Sufficient concurrent licenses for your OpenVPN connections. Each client connected in this manner will need one license unit per synchronized connection.
Configuration
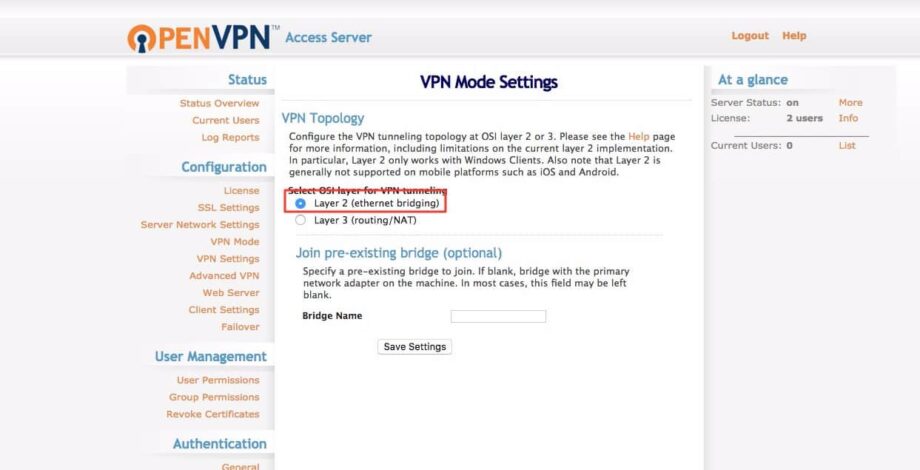
To connect your VPN client to the private network, your server must be configured in the Ethernet bridging mode and placed in the silent bridge you created previously. To connect the private bridge, login to the Admin UI, Tick VPN mode on the left navigation panel, and then identify the bridge name you have created earlier.
Afterward, go to the advanced VPN section of the Web Admin UI. Under extra OpenVPN configuration directives and inside the server configuration directive box, enter the follow line using the structure below:
ifconfig-pool <start IP address> <end IP address> <subnet mask>
The start IP address is the initial IP address you would like to assign to your connected VPN clients, the last IP address is the ending IP address available in the pool for your connected VPN clients, and the subnet mask is the mask you are assigning for this network.
For example, if you need a virtual private network with the following characteristics:
| Reserved VPN IP Range: | 192.168.1.1 – 192.168.1.253 |
| Subnet Mask: | 225.225.225.0 |
You would enter the following in the box mentioned above:
ifconfig-pool 192.168.1.1 192.168.1.253 255.255.255.0
Conversely, if you plan to assign your virtual private network server an IP address on this network, you may do so on the dynamic bridge interface, but make sure that this IP does not fall into the array you are assigning t your VPN clients. For example, if you assign 192.168.1.2 to bridge pr0, ensure your ifconfig-pool starts on the third IP address.Note: if you decide to have Windows Clients on your virtual private network, the first working IP address of the subnet is kept for the DHCP server for your VPN client. In these cases, it is highly advised that you abstain from using the first practical IP address of the subnet in query and start with the second IP address.